Hardware
iiNet mailed me a KYP USB key
I received an interesting thing in the mail yesterday, it’s a USB dongle from iiNet, a large Australian ISP. It was glued into a large postcard-type panel, and is basically a tiny USB circuit board with a plastic tab so it can be glued to larger things.

The small print says QWERTY, which seemed odd until it was revealed to be a keyboard. It also says Windows XP ≤ which I think they meant to mean ‘Windows XP or newer’ but actually means ‘Windows XP is less than or equal to’, which is sort of stupid. It is literally nonsensical, even if I think I know what they mean.
I was reluctant to plug it into the computer, for several reasons, but primarily because the accompanying postcard says that it has videos demonstrating how awesome the Australian National Broadband Network (NBN) is, and I’ve already signed on with iiNet for NBN services the moment they become available in my area. So, I’m not interested.
But the USB thing made me curious, and I looked it up. According to the postcard, it’s made by KYP, and they include a URL: kyp.com, but this page appears to have been compromised by someone, it has no content and simply sends the user to spammy sites that throw up big warnings from my content blocker. There’s another, kypsystems.com, but it’s pretty much broken, and has no images at all. I won’t link to them ’cause I don’t want your PC to be worse off for the experience. You know how to search for them if you want to check it out.
Anyway, there’s not much information about them online. Google’s trying very hard to be useless, so a search for KYP USB pinout returns a billion pages without the critical search term kyp so I wasn’t able to immediately work out what all these extra pins are for. My best guess is they’re for programming the device in the first place.
I did find this page which talks about another company (AstraZeneca) who used a similar device to send out information.

Basically, it’s a keyboard. Or at least, it pretends to be a keyboard. This is a nasty way to get a device to automatically do stuff on a modern PC. Anyone with a modern OS or with a modicum of security sense has disabled autorun on external devices, because plugging in a bit of strange hardware and immediately getting a virus sort of sucks. But since this mimics a keyboard, it’s not likely to be blocked.
Apparently (And I haven’t tried it yet) it sets itself up as a keyboard, launches a commandline and directs the user’s browser to the appropriate website. That’s assuming it’s all legit and isn’t doing anything else, but wow, how scary is this as an attack vector? It bypasses standard security and gets into some immediate threat territory. If a bad actor programmed this to install some nastyware, I doubt many users would see it coming in time to stop it.
Imagine a device that connects to your PC, and immediately downloads and runs a bit of virus code from somewhere on the internet?
That’s what I see when I look at this thing, and I tell you, it makes me a lot more cautious about ever plugging in another device, because YOW. That’s scary.
The card it came with references a number of patents, awarded and pending.
The first is GB2434228 which describes the device pretty succinctly:
Following connection to the PC, the apparatus initialises (i.e. presents or enumerates itself) as a HID keyboard and then sends to the terminal a first predefined sequence of keycodes automatically without manual interaction; the keycodes complying with the human interface device (HID) keyboard standard protocol. Each keycode represents and simulates a keystroke, such as those performed when a user strikes a key on the PC keyboard. The keycode sequence automates the direct access to content, and/or or the initiation of a task or other process.
There are more patent links from here, but they say mostly the same thing.
I won’t be plugging this thing into my PC quite yet. If you do, let me know how it goes. =)
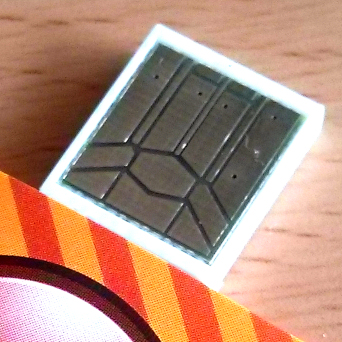
I’d very much like to know about the extra contacts on that USB connector. Can this be reprogrammed? I wonder if the fact that only the standard USB pins have vias connecting them to the other side of the circuit board is a clue that they’re not connected to anything.
Fighting with Google and finally getting some interesting results. I found this PR-babble (local mirror) which proclaims the benefits of real-time tracking, and imagines a future with miraculous new advertising campaigns based on this spoofing keyboard dongle.
Oh please.
Update!
Further research!
I plugged it in to a sacrificial system. As expected, it opened the RUN dialogue in Windows, and started typing (and not too quickly either).
The URL it points to is http://vcgw.net/M8BC/00E48F
Those last two parameters are probably the customer (iiNet and their delivery URL) and the unique ID of the key. Messing with the values seems to confirm this – changing the second has no effect on the final destination, changing the former results in a blank page.
If you check the headers on a valid value, the vcgw.net page uses a 302 (moved temporarily) redirect. I’m not sure why it doesn’t use a 301 (moved permanently), probably so the user’s browser has to check in and be tracked every time. An invalid first value results in a simple closed connection.
The key itself does install as an Apple keyboard, though it doesn’t say as much. Instead, it identifies itself as a “HID Keyboard Device”, it’s the USB vendor and product IDs that give it away: VID = 05AC, PID = 020B
These are Apple, Inc. and Pro Keyboard [Mitsumi, A1048/US layout] respectively, according to linux-usb.org.
Two drivers were installed, but one flipped by so quickly I couldn’t tell what it was. The other was a standard HID keyboard.
I wonder what happens when you plug it into a Mac.

I opened up the device and was quite happy to see that it had a real chip inside, in addition to the glop-top chip I expected. It’s a T24C02A, which is basically identical to the chip found on this page (thanks thepont). It’s probably a variant of the same chip, which means it’s a 2kB serial EEPROM. In layman’s terms, it’s 2,000 letters or numbers that can be erased and re-programmed if you have the right equipment.

Spelling it out: the glop-top chip is the USB controller and a bit of microcode that does the heavy lifting, talking to the computer and then typing in what it finds in the EEPROM chip.
According to that previous link, you can easily reprogram this, and you’ve got 2,000 characters with which to shock, annoy or compromise your friends or enemies. Cut up a standard USB device and put this in its place, why not? Take over the world, one unsuspecting victim at a time.
Thanks iiNet! This was fun. =D
--NFG
[ Feb 4 2014 ]
| Next Post | Navigation | Previous Post |
|---|
Comments
NFG
Feb 4 2014
iiNet responded to my Whirlpool post about this device, and despite sort of missing the security issue (or perhaps just skipping over it), the end result is encouraging:
That said, we’re not going to rolling out any more of these devices beyond the trial it appears NFG was included in.
I like iiNet. They’s good people (and one of the few fighting the good fight against copyright monsters in Australia.
Name:
Email:
Website:



nah
Feb 4 2014